 GFI EndPointSecurity 2013
GFI EndPointSecurity 2013
A guide to uninstall GFI EndPointSecurity 2013 from your PC
GFI EndPointSecurity 2013 is a Windows application. Read below about how to remove it from your computer. It was coded for Windows by GFI Software Ltd. Further information on GFI Software Ltd can be found here. Please follow http://www.gfi.com/ if you want to read more on GFI EndPointSecurity 2013 on GFI Software Ltd's page. EndPointSecurity.exe is the programs's main file and it takes close to 112.37 KB (115064 bytes) on disk.The executable files below are installed alongside GFI EndPointSecurity 2013. They occupy about 3.27 MB (3430576 bytes) on disk.
- EndPointSecurity.exe (112.37 KB)
- esecservice.exe (32.87 KB)
- passrecovery.exe (274.37 KB)
- scanagent.exe (232.50 KB)
- trouble.exe (1.69 MB)
- update.exe (158.37 KB)
- agentinstaller.exe (142.37 KB)
- agentinstaller64.exe (167.87 KB)
- snoozer.exe (231.87 KB)
- EndPointSecurity.exe (112.87 KB)
The information on this page is only about version 6.0.13200 of GFI EndPointSecurity 2013. GFI EndPointSecurity 2013 has the habit of leaving behind some leftovers.
Folders remaining:
- C:\Program Files (x86)\GFI\EndPointSecurity 6
- C:\Users\%user%\AppData\Local\Temp\GFI EndPointSecurity
Files remaining:
- C:\Program Files (x86)\GFI\EndPointSecurity 6\Agent\agentinstaller.exe
- C:\Program Files (x86)\GFI\EndPointSecurity 6\Agent\agentinstaller64.exe
- C:\Program Files (x86)\GFI\EndPointSecurity 6\Agent\Commands1b12889c-0c7e-47be-a450-7f32a2c29df8.tmp
- C:\Program Files (x86)\GFI\EndPointSecurity 6\Agent\EndPointSecurityAgent.msi
- C:\Program Files (x86)\GFI\EndPointSecurity 6\Agent\snoozer.exe
- C:\Program Files (x86)\GFI\EndPointSecurity 6\autocheck2.dll
- C:\Program Files (x86)\GFI\EndPointSecurity 6\commonutils.dll
- C:\Program Files (x86)\GFI\EndPointSecurity 6\crmiini.xml
- C:\Program Files (x86)\GFI\EndPointSecurity 6\cryptcom.dll
- C:\Program Files (x86)\GFI\EndPointSecurity 6\Data\deployment_history.xml
- C:\Program Files (x86)\GFI\EndPointSecurity 6\Data\Dictionaries\Diseases.dct
- C:\Program Files (x86)\GFI\EndPointSecurity 6\Data\Dictionaries\Drugs.dct
- C:\Program Files (x86)\GFI\EndPointSecurity 6\Data\Dictionaries\Hazardous Materials.dct
- C:\Program Files (x86)\GFI\EndPointSecurity 6\Data\Dictionaries\Racial Slurs.dct
- C:\Program Files (x86)\GFI\EndPointSecurity 6\Data\Dictionaries\Trivial Language.dct
- C:\Program Files (x86)\GFI\EndPointSecurity 6\Data\General\branding.xml
- C:\Program Files (x86)\GFI\EndPointSecurity 6\Data\General\modulestrings.xml
- C:\Program Files (x86)\GFI\EndPointSecurity 6\Data\msgstorage.dat
- C:\Program Files (x86)\GFI\EndPointSecurity 6\Data\opspplugins.dep
- C:\Program Files (x86)\GFI\EndPointSecurity 6\Data\Policies\4b51ebf783d84ff9965a5db0f7b2be0c.txt
- C:\Program Files (x86)\GFI\EndPointSecurity 6\Data\Policies\4b51ebf783d84ff9965a5db0f7b2be0c.xml
- C:\Program Files (x86)\GFI\EndPointSecurity 6\Data\Reports\css\base.css
- C:\Program Files (x86)\GFI\EndPointSecurity 6\Data\Reports\css\main.css
- C:\Program Files (x86)\GFI\EndPointSecurity 6\Data\Reports\css\reset.css
- C:\Program Files (x86)\GFI\EndPointSecurity 6\Data\Reports\errorreport.xsl
- C:\Program Files (x86)\GFI\EndPointSecurity 6\Data\Reports\Images\arrowdown.gif
- C:\Program Files (x86)\GFI\EndPointSecurity 6\Data\Reports\Images\arrowup.gif
- C:\Program Files (x86)\GFI\EndPointSecurity 6\Data\Reports\Images\background.png
- C:\Program Files (x86)\GFI\EndPointSecurity 6\Data\Reports\Images\cnotprot.gif
- C:\Program Files (x86)\GFI\EndPointSecurity 6\Data\Reports\Images\cnotscan.gif
- C:\Program Files (x86)\GFI\EndPointSecurity 6\Data\Reports\Images\cprot.gif
- C:\Program Files (x86)\GFI\EndPointSecurity 6\Data\Reports\Images\dottedbox.gif
- C:\Program Files (x86)\GFI\EndPointSecurity 6\Data\Reports\Images\endpointscanpowered.gif
- C:\Program Files (x86)\GFI\EndPointSecurity 6\Data\Reports\Images\escan_esec.gif
- C:\Program Files (x86)\GFI\EndPointSecurity 6\Data\Reports\Images\horline.gif
- C:\Program Files (x86)\GFI\EndPointSecurity 6\Data\Reports\Images\iDevice1.gif
- C:\Program Files (x86)\GFI\EndPointSecurity 6\Data\Reports\Images\iDevice10.gif
- C:\Program Files (x86)\GFI\EndPointSecurity 6\Data\Reports\Images\iDevice2.gif
- C:\Program Files (x86)\GFI\EndPointSecurity 6\Data\Reports\Images\iDevice3.gif
- C:\Program Files (x86)\GFI\EndPointSecurity 6\Data\Reports\Images\iDevice4.gif
- C:\Program Files (x86)\GFI\EndPointSecurity 6\Data\Reports\Images\iDevice5.gif
- C:\Program Files (x86)\GFI\EndPointSecurity 6\Data\Reports\Images\iDevice6.gif
- C:\Program Files (x86)\GFI\EndPointSecurity 6\Data\Reports\Images\iDevice7.gif
- C:\Program Files (x86)\GFI\EndPointSecurity 6\Data\Reports\Images\iDevice8.gif
- C:\Program Files (x86)\GFI\EndPointSecurity 6\Data\Reports\Images\iDevice9.gif
- C:\Program Files (x86)\GFI\EndPointSecurity 6\Data\Reports\Images\lg_gfi.gif
- C:\Program Files (x86)\GFI\EndPointSecurity 6\Data\Reports\Images\logo.png
- C:\Program Files (x86)\GFI\EndPointSecurity 6\Data\Reports\Images\minus.gif
- C:\Program Files (x86)\GFI\EndPointSecurity 6\Data\Reports\Images\plus.gif
- C:\Program Files (x86)\GFI\EndPointSecurity 6\Data\Reports\Images\PROP13C.jpg
- C:\Program Files (x86)\GFI\EndPointSecurity 6\Data\Reports\Images\redbox4.gif
- C:\Program Files (x86)\GFI\EndPointSecurity 6\Data\Reports\Images\risklevel0.gif
- C:\Program Files (x86)\GFI\EndPointSecurity 6\Data\Reports\Images\risklevel1.gif
- C:\Program Files (x86)\GFI\EndPointSecurity 6\Data\Reports\Images\risklevel10.gif
- C:\Program Files (x86)\GFI\EndPointSecurity 6\Data\Reports\Images\risklevel2.gif
- C:\Program Files (x86)\GFI\EndPointSecurity 6\Data\Reports\Images\risklevel3.gif
- C:\Program Files (x86)\GFI\EndPointSecurity 6\Data\Reports\Images\risklevel4.gif
- C:\Program Files (x86)\GFI\EndPointSecurity 6\Data\Reports\Images\risklevel5.gif
- C:\Program Files (x86)\GFI\EndPointSecurity 6\Data\Reports\Images\risklevel6.gif
- C:\Program Files (x86)\GFI\EndPointSecurity 6\Data\Reports\Images\risklevel7.gif
- C:\Program Files (x86)\GFI\EndPointSecurity 6\Data\Reports\Images\risklevel8.gif
- C:\Program Files (x86)\GFI\EndPointSecurity 6\Data\Reports\Images\risklevel9.gif
- C:\Program Files (x86)\GFI\EndPointSecurity 6\Data\Reports\Images\rlevel0.gif
- C:\Program Files (x86)\GFI\EndPointSecurity 6\Data\Reports\Images\rlevel1.gif
- C:\Program Files (x86)\GFI\EndPointSecurity 6\Data\Reports\Images\rlevel10.gif
- C:\Program Files (x86)\GFI\EndPointSecurity 6\Data\Reports\Images\rlevel2.gif
- C:\Program Files (x86)\GFI\EndPointSecurity 6\Data\Reports\Images\rlevel3.gif
- C:\Program Files (x86)\GFI\EndPointSecurity 6\Data\Reports\Images\rlevel4.gif
- C:\Program Files (x86)\GFI\EndPointSecurity 6\Data\Reports\Images\rlevel5.gif
- C:\Program Files (x86)\GFI\EndPointSecurity 6\Data\Reports\Images\rlevel6.gif
- C:\Program Files (x86)\GFI\EndPointSecurity 6\Data\Reports\Images\rlevel7.gif
- C:\Program Files (x86)\GFI\EndPointSecurity 6\Data\Reports\Images\rlevel8.gif
- C:\Program Files (x86)\GFI\EndPointSecurity 6\Data\Reports\Images\rlevel9.gif
- C:\Program Files (x86)\GFI\EndPointSecurity 6\Data\Reports\Images\TableHeaderRepeat.png
- C:\Program Files (x86)\GFI\EndPointSecurity 6\Data\Reports\Images\vertline.gif
- C:\Program Files (x86)\GFI\EndPointSecurity 6\Data\Reports\js\MochiKit\Async.js
- C:\Program Files (x86)\GFI\EndPointSecurity 6\Data\Reports\js\MochiKit\Base.js
- C:\Program Files (x86)\GFI\EndPointSecurity 6\Data\Reports\js\MochiKit\Color.js
- C:\Program Files (x86)\GFI\EndPointSecurity 6\Data\Reports\js\MochiKit\DateTime.js
- C:\Program Files (x86)\GFI\EndPointSecurity 6\Data\Reports\js\MochiKit\DOM.js
- C:\Program Files (x86)\GFI\EndPointSecurity 6\Data\Reports\js\MochiKit\Format.js
- C:\Program Files (x86)\GFI\EndPointSecurity 6\Data\Reports\js\MochiKit\Iter.js
- C:\Program Files (x86)\GFI\EndPointSecurity 6\Data\Reports\js\MochiKit\Logging.js
- C:\Program Files (x86)\GFI\EndPointSecurity 6\Data\Reports\js\MochiKit\LoggingPane.js
- C:\Program Files (x86)\GFI\EndPointSecurity 6\Data\Reports\js\MochiKit\MochiKit.js
- C:\Program Files (x86)\GFI\EndPointSecurity 6\Data\Reports\js\MochiKit\Signal.js
- C:\Program Files (x86)\GFI\EndPointSecurity 6\Data\Reports\js\MochiKit\Visual.js
- C:\Program Files (x86)\GFI\EndPointSecurity 6\Data\Reports\js\PlotKit\excanvas.js
- C:\Program Files (x86)\GFI\EndPointSecurity 6\Data\Reports\js\PlotKit\PlotKit_Packed.js
- C:\Program Files (x86)\GFI\EndPointSecurity 6\Data\Reports\js\sorttable.js
- C:\Program Files (x86)\GFI\EndPointSecurity 6\Data\Reports\report.xsl
- C:\Program Files (x86)\GFI\EndPointSecurity 6\Data\ScanResults\ScanResult_20190626_1.xml
- C:\Program Files (x86)\GFI\EndPointSecurity 6\Data\ScanResults\ScanResult_20190626_2.xml
- C:\Program Files (x86)\GFI\EndPointSecurity 6\Data\ScanResults\ScanResult_20190626_3.xml
- C:\Program Files (x86)\GFI\EndPointSecurity 6\Data\ScanResults\ScanResult_20190626_4.xml
- C:\Program Files (x86)\GFI\EndPointSecurity 6\Data\ScanResults\ScanResult_current.xml
- C:\Program Files (x86)\GFI\EndPointSecurity 6\Data\toolcfg_accessCodes.xml
- C:\Program Files (x86)\GFI\EndPointSecurity 6\Data\toolcfg_activityLog.xml
- C:\Program Files (x86)\GFI\EndPointSecurity 6\Data\toolcfg_advancedSettings.xml
- C:\Program Files (x86)\GFI\EndPointSecurity 6\Data\toolcfg_alertingoptions.xml
Registry keys:
- HKEY_CLASSES_ROOT\Installer\Assemblies\C:|Program Files (x86)|GFI|EndPointSecurity 6|commonutils.dll
- HKEY_CLASSES_ROOT\Installer\Assemblies\C:|Program Files (x86)|GFI|EndPointSecurity 6|divelements.sandgrid.dll
- HKEY_CLASSES_ROOT\Installer\Assemblies\C:|Program Files (x86)|GFI|EndPointSecurity 6|dundaswinchart.dll
- HKEY_CLASSES_ROOT\Installer\Assemblies\C:|Program Files (x86)|GFI|EndPointSecurity 6|EndPointSecurity.exe
- HKEY_CLASSES_ROOT\Installer\Assemblies\C:|Program Files (x86)|GFI|EndPointSecurity 6|eseccrmi.dll
- HKEY_CLASSES_ROOT\Installer\Assemblies\C:|Program Files (x86)|GFI|EndPointSecurity 6|gfiappframework.dll
- HKEY_CLASSES_ROOT\Installer\Assemblies\C:|Program Files (x86)|GFI|EndPointSecurity 6|gfilogging.dll
- HKEY_CLASSES_ROOT\Installer\Assemblies\C:|Program Files (x86)|GFI|EndPointSecurity 6|impex.dll
- HKEY_CLASSES_ROOT\Installer\Assemblies\C:|Program Files (x86)|GFI|EndPointSecurity 6|Ionic.Zip.Reduced.dll
- HKEY_CLASSES_ROOT\Installer\Assemblies\C:|Program Files (x86)|GFI|EndPointSecurity 6|NDesk.Options.dll
- HKEY_CLASSES_ROOT\Installer\Assemblies\C:|Program Files (x86)|GFI|EndPointSecurity 6|objectpickerhlp.dll
- HKEY_CLASSES_ROOT\Installer\Assemblies\C:|Program Files (x86)|GFI|EndPointSecurity 6|opalerting.dll
- HKEY_CLASSES_ROOT\Installer\Assemblies\C:|Program Files (x86)|GFI|EndPointSecurity 6|opautoprotect.dll
- HKEY_CLASSES_ROOT\Installer\Assemblies\C:|Program Files (x86)|GFI|EndPointSecurity 6|opcommon.dll
- HKEY_CLASSES_ROOT\Installer\Assemblies\C:|Program Files (x86)|GFI|EndPointSecurity 6|opdboperations.dll
- HKEY_CLASSES_ROOT\Installer\Assemblies\C:|Program Files (x86)|GFI|EndPointSecurity 6|opdeployment.dll
- HKEY_CLASSES_ROOT\Installer\Assemblies\C:|Program Files (x86)|GFI|EndPointSecurity 6|opstatusmonitor.dll
- HKEY_CLASSES_ROOT\Installer\Assemblies\C:|Program Files (x86)|GFI|EndPointSecurity 6|opstatusmonitorcomm.dll
- HKEY_CLASSES_ROOT\Installer\Assemblies\C:|Program Files (x86)|GFI|EndPointSecurity 6|optempaccess.dll
- HKEY_CLASSES_ROOT\Installer\Assemblies\C:|Program Files (x86)|GFI|EndPointSecurity 6|plactivitylog.dll
- HKEY_CLASSES_ROOT\Installer\Assemblies\C:|Program Files (x86)|GFI|EndPointSecurity 6|plcomputers.dll
- HKEY_CLASSES_ROOT\Installer\Assemblies\C:|Program Files (x86)|GFI|EndPointSecurity 6|plconfigadvanced.dll
- HKEY_CLASSES_ROOT\Installer\Assemblies\C:|Program Files (x86)|GFI|EndPointSecurity 6|plconfigalerts.dll
- HKEY_CLASSES_ROOT\Installer\Assemblies\C:|Program Files (x86)|GFI|EndPointSecurity 6|plconfigdatabase.dll
- HKEY_CLASSES_ROOT\Installer\Assemblies\C:|Program Files (x86)|GFI|EndPointSecurity 6|plconfiggroups.dll
- HKEY_CLASSES_ROOT\Installer\Assemblies\C:|Program Files (x86)|GFI|EndPointSecurity 6|plconfigmessages.dll
- HKEY_CLASSES_ROOT\Installer\Assemblies\C:|Program Files (x86)|GFI|EndPointSecurity 6|plconfigqsw.dll
- HKEY_CLASSES_ROOT\Installer\Assemblies\C:|Program Files (x86)|GFI|EndPointSecurity 6|plconfigurations.dll
- HKEY_CLASSES_ROOT\Installer\Assemblies\C:|Program Files (x86)|GFI|EndPointSecurity 6|plconfigusers.dll
- HKEY_CLASSES_ROOT\Installer\Assemblies\C:|Program Files (x86)|GFI|EndPointSecurity 6|plcreategroups.dll
- HKEY_CLASSES_ROOT\Installer\Assemblies\C:|Program Files (x86)|GFI|EndPointSecurity 6|pldevicescan.dll
- HKEY_CLASSES_ROOT\Installer\Assemblies\C:|Program Files (x86)|GFI|EndPointSecurity 6|pleditlic.dll
- HKEY_CLASSES_ROOT\Installer\Assemblies\C:|Program Files (x86)|GFI|EndPointSecurity 6|plgeneral.dll
- HKEY_CLASSES_ROOT\Installer\Assemblies\C:|Program Files (x86)|GFI|EndPointSecurity 6|pllogbrowser.dll
- HKEY_CLASSES_ROOT\Installer\Assemblies\C:|Program Files (x86)|GFI|EndPointSecurity 6|plobjectpickerusers.dll
- HKEY_CLASSES_ROOT\Installer\Assemblies\C:|Program Files (x86)|GFI|EndPointSecurity 6|plprotectionpolicies.dll
- HKEY_CLASSES_ROOT\Installer\Assemblies\C:|Program Files (x86)|GFI|EndPointSecurity 6|plreporter.dll
- HKEY_CLASSES_ROOT\Installer\Assemblies\C:|Program Files (x86)|GFI|EndPointSecurity 6|plstatusagents.dll
- HKEY_CLASSES_ROOT\Installer\Assemblies\C:|Program Files (x86)|GFI|EndPointSecurity 6|plstatusdeployment.dll
- HKEY_CLASSES_ROOT\Installer\Assemblies\C:|Program Files (x86)|GFI|EndPointSecurity 6|plstatusgeneral.dll
- HKEY_CLASSES_ROOT\Installer\Assemblies\C:|Program Files (x86)|GFI|EndPointSecurity 6|plstatusstatistics.dll
- HKEY_CLASSES_ROOT\Installer\Assemblies\C:|Program Files (x86)|GFI|EndPointSecurity 6|update.exe
- HKEY_LOCAL_MACHINE\SOFTWARE\Classes\Installer\Products\11114D1094251A5468B4B11A1FDD2253
- HKEY_LOCAL_MACHINE\Software\GFI\EndPointSecurity6
- HKEY_LOCAL_MACHINE\Software\Microsoft\Windows\CurrentVersion\Uninstall\{01D41111-5249-45A1-864B-1BA1F1DD2235}
Additional registry values that are not removed:
- HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\MuiCache\C:\Program Files (x86)\GFI\EndPointSecurity 6\trouble.exe
- HKEY_LOCAL_MACHINE\SOFTWARE\Classes\Installer\Products\11114D1094251A5468B4B11A1FDD2253\ProductName
- HKEY_LOCAL_MACHINE\System\CurrentControlSet\Services\EsecSvc\ImagePath
A way to delete GFI EndPointSecurity 2013 with the help of Advanced Uninstaller PRO
GFI EndPointSecurity 2013 is an application offered by the software company GFI Software Ltd. Frequently, people decide to remove this program. This can be hard because doing this manually requires some skill related to Windows program uninstallation. The best SIMPLE action to remove GFI EndPointSecurity 2013 is to use Advanced Uninstaller PRO. Here are some detailed instructions about how to do this:1. If you don't have Advanced Uninstaller PRO already installed on your system, add it. This is good because Advanced Uninstaller PRO is one of the best uninstaller and all around tool to optimize your system.
DOWNLOAD NOW
- go to Download Link
- download the setup by clicking on the DOWNLOAD NOW button
- install Advanced Uninstaller PRO
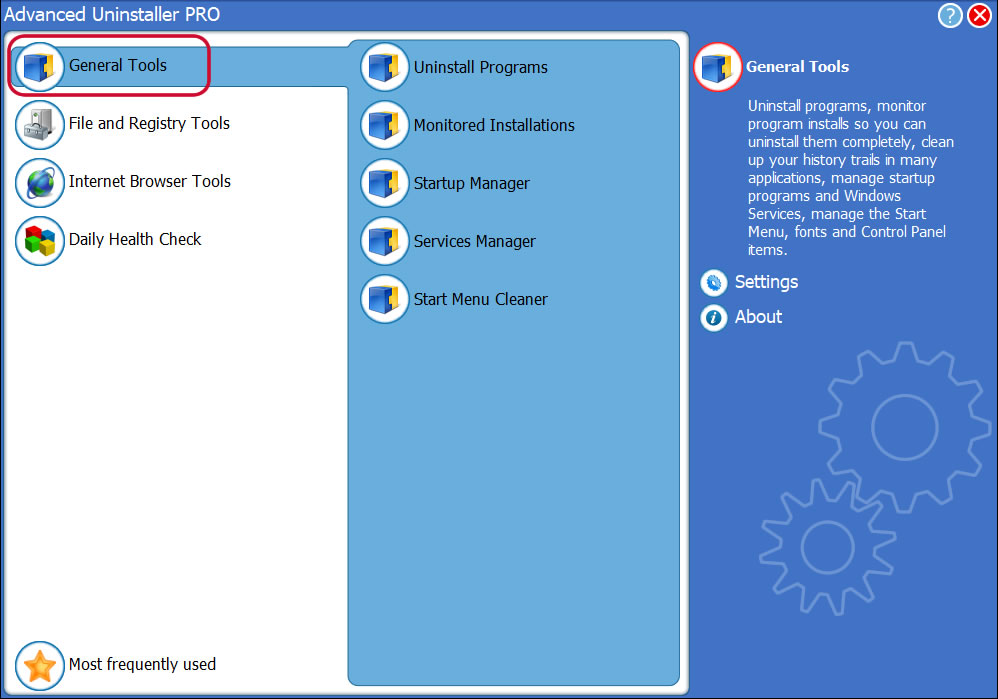
3. Click on the General Tools button
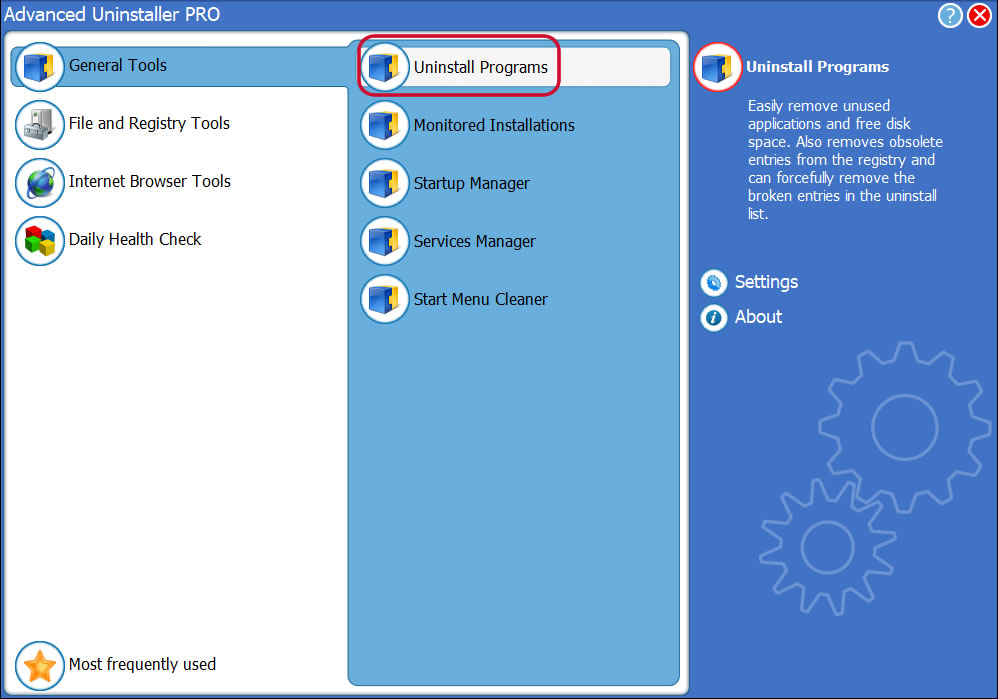
4. Click on the Uninstall Programs button
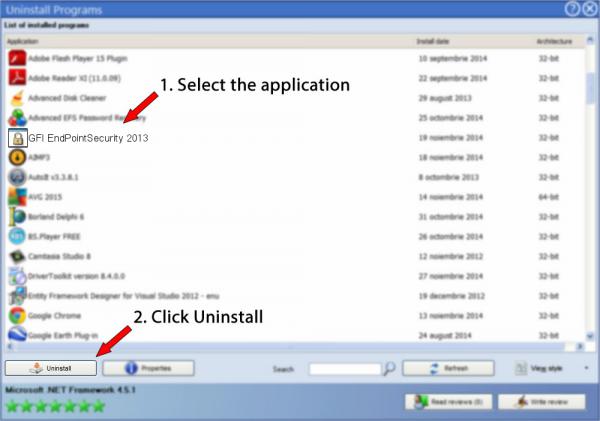
5. All the programs existing on your PC will appear
6. Navigate the list of programs until you locate GFI EndPointSecurity 2013 or simply click the Search field and type in "GFI EndPointSecurity 2013". If it exists on your system the GFI EndPointSecurity 2013 app will be found automatically. Notice that after you click GFI EndPointSecurity 2013 in the list of applications, some data about the application is available to you:
- Star rating (in the lower left corner). The star rating explains the opinion other users have about GFI EndPointSecurity 2013, from "Highly recommended" to "Very dangerous".
- Opinions by other users - Click on the Read reviews button.
- Technical information about the program you are about to uninstall, by clicking on the Properties button.
8. After removing GFI EndPointSecurity 2013, Advanced Uninstaller PRO will ask you to run a cleanup. Click Next to proceed with the cleanup. All the items that belong GFI EndPointSecurity 2013 that have been left behind will be detected and you will be able to delete them. By removing GFI EndPointSecurity 2013 with Advanced Uninstaller PRO, you can be sure that no Windows registry items, files or directories are left behind on your disk.
Your Windows PC will remain clean, speedy and ready to serve you properly.
Geographical user distribution
Disclaimer
This page is not a piece of advice to remove GFI EndPointSecurity 2013 by GFI Software Ltd from your PC, we are not saying that GFI EndPointSecurity 2013 by GFI Software Ltd is not a good application. This text only contains detailed instructions on how to remove GFI EndPointSecurity 2013 supposing you decide this is what you want to do. Here you can find registry and disk entries that our application Advanced Uninstaller PRO stumbled upon and classified as "leftovers" on other users' computers.
2016-08-01 / Written by Andreea Kartman for Advanced Uninstaller PRO
follow @DeeaKartmanLast update on: 2016-08-01 13:26:12.147

